project aeon
Anonymous Encapsulation Over Nameservice

Anonymity networks like Tor fail to provide perfect anonymity due to some technical
drawbacks they are not able to deal with, caused by underlying technologies.
Names are converted into IP adresses using the local DNS resolver of the system.
Since this happens before the connection itself is forwarded to the anonymity network,
the name of the requested resource may be exposed to an observer.
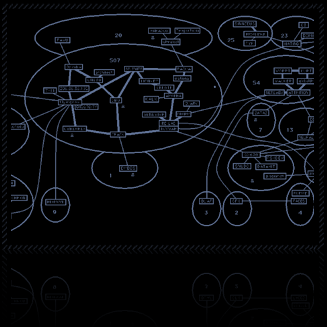
This project aims to provide anonymous DNS lookups by encrypting requests and responses
and sending them using DNS tunneling through an unauthoritative nameserver to the delegated
server that supports aeon
Due to the usage of encryption and relaying techniques (recursive requests) neither the
server knows who requested the information nor the relaying unauthoritative nameserver
knows what kind of information was requested or returned.

Right now, research has to be done to the topic.
We're crafting a proof-of-concept to get a clue about
performance and security (and of course availability) issues.
A possible software workflow can be downloaded at the papers-
and downloads block on the right.
|
|